How to Prevent Flash Loan Exploits in DeFi Protocols
 Mar, 20 2026
Mar, 20 2026
Flash loans have changed how DeFi works. They let anyone borrow millions of dollars in crypto - with no collateral - as long as the whole transaction finishes in one block. Sounds useful? It is. But it’s also become the go-to tool for hackers. In 2025 alone, flash loan attacks stole over $1.7 billion. That’s more than all of 2024. And it’s not slowing down. If you’re running or investing in a DeFi protocol, ignoring flash loan risks isn’t an option. It’s a recipe for disaster.
How Flash Loan Attacks Actually Work
It’s not magic. It’s math - and bad code.
Here’s the basic flow:
- An attacker takes out a flash loan - say, $50 million in DAI - from Aave or dYdX.
- They use that money to buy up a small token on a DEX like Uniswap, driving its price way up.
- They swap that inflated token for another asset - say, ETH - on a different DEX where the price hasn’t caught up yet.
- They repay the original loan, pocketing the difference as profit.
The whole thing happens in one block. No one sees it coming. No time to react. And because the loan is repaid instantly, there’s no trace of debt. Just clean, untraceable profit.
But it gets worse. Attackers don’t just manipulate prices. They:
- Swap collateral in lending protocols to replace real assets with fake ones.
- Use borrowed governance tokens to vote on malicious proposals - like draining treasury funds.
- Exploit oracle feeds that rely on single-price sources, like a DEX with low liquidity.
The Euler Finance hack in 2023? $197 million gone because a function called DonateToReserve didn’t check if the donated token’s price was real. The attacker used a flash loan to inflate the token’s value, donated it, and withdrew real ETH. Simple. Brutal.
What Makes Flash Loans So Dangerous?
It’s not the loan. It’s the atomicity.
Every blockchain transaction is either fully successful or fully rolled back. Flash loans use that rule to their advantage. If any step fails - say, the price doesn’t move enough - the whole transaction cancels. No loss. No penalty. Just try again.
This means attackers can test dozens of attack patterns in minutes. They don’t need to fund a wallet. They don’t need to wait for liquidity. They just write code, deploy it, and let the blockchain do the rest.
And here’s the kicker: most smart contracts weren’t built to handle this. They assume prices are stable. They assume collateral is real. They assume users aren’t trying to game the system. That’s why 76% of DeFi hacks in 2025 involved flash loans.
Top 4 Attack Vectors You Must Defend Against
Not all flash loan attacks are the same. Here are the four most common - and how to stop them.
1. Price Manipulation
This is the #1 attack. Attackers flood a low-liquidity pool with borrowed tokens, spike the price, then cash out.
Fix: Use time-weighted average price (TWAP) oracles. Don’t rely on single-point prices. If a token’s price jumps 40% in one block, that’s not market movement - it’s an attack. Your contract should reject any price change over 15% in a single block.
2. Collateral Swapping
Attackers borrow tokens, deposit them as collateral in a lending protocol, then withdraw more than they should because the system thinks the asset is worth more than it is.
Fix: Require collateral to be verified by at least two independent oracles. Add a delay between collateral deposit and loan issuance. If a user deposits a token and immediately borrows 10x its value - pause. Investigate.
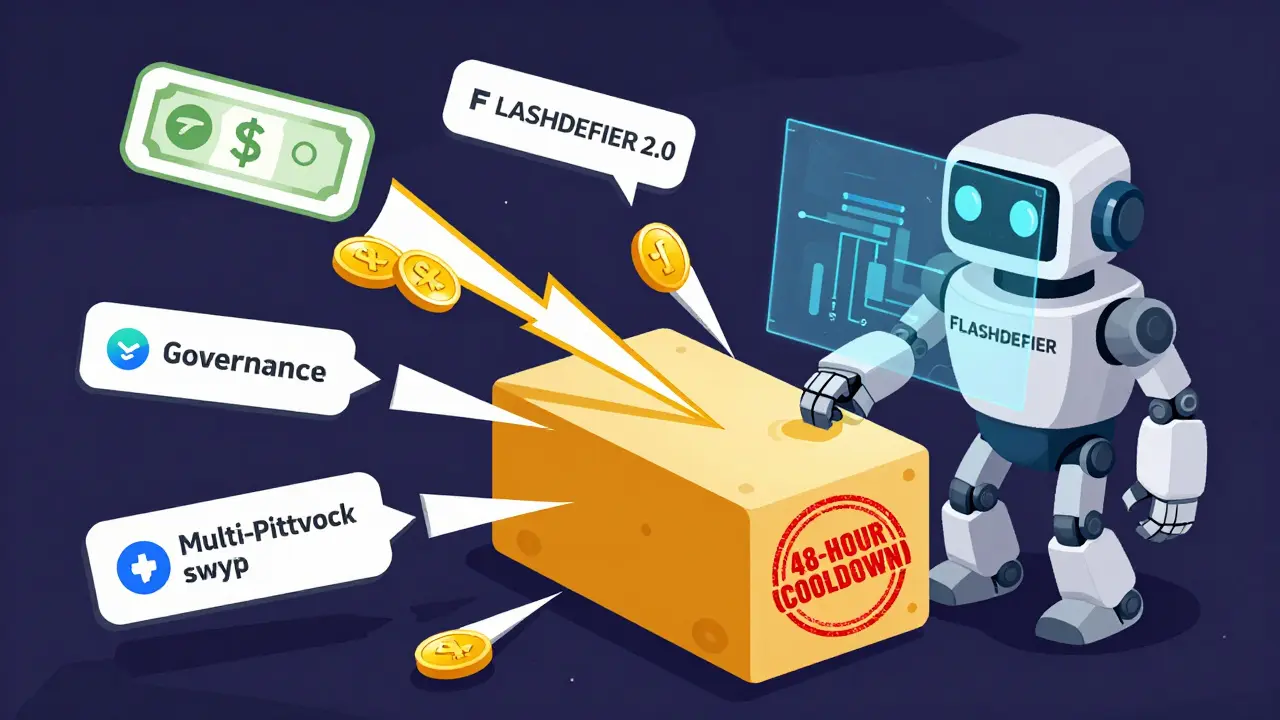
3. Governance Takeovers
Flash loans let attackers temporarily hold enough governance tokens to vote themselves into control. They change treasury rules, drain funds, then repay the loan.
Fix: Implement vote delegation delays. Require a 48-hour cooldown between voting power changes and execution. Also, limit voting power per wallet - even if someone borrows 10 million tokens, they shouldn’t get 10 million votes.
4. Cross-Protocol Arbitrage
Attackers exploit price gaps between protocols. For example, buy low on Curve, sell high on Uniswap, repay loan, profit.
Fix: Monitor for unusual transaction patterns. If the same wallet interacts with three different DEXs in one block - flag it. Use tools like FlashDeFier to build call graphs and spot suspicious sequences.

How to Build Real Prevention - Not Just Band-Aids
Static audits aren’t enough. You can’t just hire a firm to check your code once and call it done. Flash loan attacks evolve faster than your audit cycle.
You need a layered defense:
- Static Analysis: Use tools like FlashDeFier is an advanced static analysis tool developed by Ka Wai Wu at Virginia Tech that detects flash loan-induced price manipulation vulnerabilities by mapping inter-contract data flows. It’s the only tool that tracks how data moves between contracts - not just what’s in one contract. It found 30% more vulnerabilities than older tools like DeFiTainter.
- Dynamic Monitoring: Set up real-time alerts for price spikes, collateral changes, and multi-protocol interactions. If a token’s price jumps 25% in 30 seconds, freeze withdrawals. Investigate.
- Smart Contract Audits: Don’t just audit once. Audit every major upgrade. Use auditors who specialize in DeFi - not just general blockchain firms.
- Protocol-Level Limits: Cap flash loan sizes. Limit how much can be borrowed from a single pool in one block. Require a small fee for flash loans - even 0.01% deters automated attacks.
The Zunami Protocol attack in 2024? $2.1 million lost because they didn’t limit how much could be borrowed from their stablecoin pool. They assumed users wouldn’t abuse it. They were wrong.
What’s Working Right Now? Real Tools, Real Results
There’s no silver bullet. But some tools are making a difference.
FlashDeFier - as mentioned - leads the pack. It’s open-source, free, and built on advanced taint analysis. It doesn’t just look for known patterns. It learns how data flows between contracts. If a token’s price is used in a loan calculation, and that price came from a DEX with low liquidity - it flags it.
OWASP SC07:2025 - the official classification for flash loan exploits - now requires protocols to document how they prevent these attacks. If you’re building a DeFi product, you’re expected to follow these guidelines. Ignoring them means you won’t get insurance. You won’t get institutional investors.
DeFi security firms like Aon and FraudNet now offer real-time monitoring dashboards that track cross-chain flash loan behavior. They don’t just alert you - they show you the full attack chain: which DEXs were used, which oracles were manipulated, and how the profit was withdrawn.
And yes - the market is responding. DeFi security spending jumped 340% between 2024 and 2025. Flash loan-specific tools now make up 15% of that spend. That’s not a trend. That’s a wake-up call.
What’s Coming Next? The Future of Prevention
FlashDeFier 2.0 is coming in Q2 2025. It adds machine learning to predict attack patterns before they happen. Think of it like a fraud detector for crypto - trained on 10,000 past attacks.
There are also new EIPs (Ethereum Improvement Proposals) under review that would:
- Require flash loans to include a unique transaction signature.
- Limit flash loan amounts based on a protocol’s liquidity depth.
- Force oracles to provide historical price ranges, not just current values.
Long-term, the industry will standardize. Protocols that don’t adopt these measures will be seen as high-risk. Insurance companies will refuse to cover them. Investors will walk away.
Final Checklist: Are You Protected?
Here’s what you need to do - right now:
- ✅ Replace single-point price oracles with TWAP or multi-source oracles.
- ✅ Implement transaction limits on flash loans - both per transaction and per block.
- ✅ Add delays for collateral changes and governance votes.
- ✅ Integrate FlashDeFier or a similar tool into your CI/CD pipeline.
- ✅ Set up real-time alerts for price spikes, large collateral deposits, and multi-protocol swaps.
- ✅ Audit your code every time you upgrade - not once a year.
If you’re not doing all six - you’re vulnerable. And in DeFi, vulnerability isn’t a risk. It’s a countdown.
What exactly is a flash loan?
A flash loan is a type of uncollateralized loan in DeFi that allows users to borrow cryptocurrency - often millions of dollars - as long as the entire transaction, including borrowing, using the funds, and repaying the loan, completes within a single blockchain block. If any part fails, the whole transaction is reversed, so the lender never risks losing funds.
Why are flash loans so dangerous for DeFi protocols?
Flash loans are dangerous because they let attackers manipulate prices, swap collateral, or hijack governance systems without putting up any of their own money. Since the entire attack happens in one block and is repaid instantly, there’s no trace of debt - just profit. Many protocols weren’t designed to handle this kind of atomic, high-speed manipulation.
Can traditional smart contract audits stop flash loan attacks?
No. Traditional audits check code for bugs - like reentrancy or integer overflows. But flash loan attacks exploit how contracts interact with each other under abnormal conditions. An audit might say your code is fine, but if it uses a single-price oracle during a flash loan, it’s still vulnerable. You need specialized tools like FlashDeFier that analyze data flows across multiple contracts.
What’s the most effective prevention tool available today?
FlashDeFier, developed by Ka Wai Wu at Virginia Tech, is currently the most effective tool. It uses enhanced static taint analysis to trace how data moves between contracts - identifying hidden price manipulation paths that other tools miss. It’s open-source, free, and detects 76.4% of flash loan vulnerabilities - a 30% improvement over older tools.
Are flash loans illegal or banned?
No, flash loans aren’t illegal. They’re a legitimate DeFi feature used for arbitrage, collateral swaps, and liquidity provision. The problem isn’t the loan itself - it’s how attackers abuse it. The industry is moving toward regulation that requires protocols to implement safeguards, not ban the feature entirely.
How can small DeFi projects afford flash loan prevention?
You don’t need expensive tools. Start with free ones: use FlashDeFier for static analysis, switch to TWAP oracles (open-source implementations exist), and add basic transaction limits. Most attacks target large protocols with high liquidity. A small project with simple logic and capped loan sizes is rarely targeted - if you’ve done the basics right.
Sahithi Reddy
March 20, 2026 AT 08:54innovate through exploitation
Lauren J. Walter
March 20, 2026 AT 11:20lol
George Hutchings
March 22, 2026 AT 06:18it's that everyone thinks they're a dev
and nobody tests edge cases
just slap on a TWAP and call it a day
Henrique Lyma
March 24, 2026 AT 04:34like putting duct tape on a nuclear reactor and calling it 'improved safety'
FlashDeFier? cute
the real solution is banning flash loans entirely
or better yet - make them illegal
because clearly, the market can't self-regulate when humans are involved
Steph Andrews
March 24, 2026 AT 06:27but maybe we're overcomplicating it
not every protocol needs to be a bank
if you're small and simple - you're probably fine
don't try to be aave
Prakash Patel
March 25, 2026 AT 00:36and this is just the market filtering out bad code
maybe we should stop trying to protect people from their own dumb contracts
Zachary N
March 26, 2026 AT 03:42it's not optional anymore
the tool finds vulnerabilities you didn't even know existed
like that one function that trusted a price from a pool with $20k liquidity
you think it's fine until someone drains $197M
and then you're on Twitter explaining why you didn't listen
don't be that guy
Elizabeth Kurtz
March 26, 2026 AT 13:48but honestly
most devs don't even know what a TWAP is
so telling them to use it is like telling a toddler to fix a transmission
we need better education
not just tools
Marc Morgan
March 28, 2026 AT 04:02cool
guess i'll go back to trading memecoins
Graham Smith
March 29, 2026 AT 11:46it's not merely static analysis
it's dynamic semantic tracing with graph-theoretic modeling of value propagation
most audit firms still operate in the 2020 era
they're analyzing syntax, not semantics
Katrina Smith
March 30, 2026 AT 15:18Anastasia Danavath
March 30, 2026 AT 20:23anshika garg
March 31, 2026 AT 18:09but why we built a financial system where a single block can erase a billion dollars
is this innovation
or just chaos with a whitepaper
Bruce Doucette
April 1, 2026 AT 16:41wait until the fed starts issuing a CBDC
then watch how fast these attacks scale
you're not ready
no one is
Gene Inoue
April 2, 2026 AT 07:12you can't prevent stupidity
you can only make it expensive
so charge 1% fee
and let the market sort it out
Ricky Fairlamb
April 3, 2026 AT 16:38the real attack vector isn't flash loans
it's the fact that people believe in 'decentralized' systems
when every oracle is controlled by 3 companies
and every 'open-source' tool is maintained by one guy in his basement
we're not building finance
we're building a cult with code
Tony Weaver
April 4, 2026 AT 14:32what if they front-run your fee mechanism?
what if the oracle they manipulate is the one you're using for governance?
your checklist is a joke
you're not securing a protocol
you're playing whack-a-mole with a sledgehammer
Patty Atima
April 5, 2026 AT 12:26Lucy de Gruchy
April 6, 2026 AT 07:50the real threat is the fed
they're using flash loan attacks to test how fast they can collapse crypto
it's not hackers
it's central banks
wake up
Carol Lueneburg
April 7, 2026 AT 05:24every protocol that survives this is going to be stronger
and honestly?
we need that
the bad ones deserve to burn
Ernestine La Baronne Orange
April 8, 2026 AT 08:11Manali Sovani
April 8, 2026 AT 10:58